Difference between revisions of "Cloud Computing"
Adelo Vieira (talk | contribs) |
Adelo Vieira (talk | contribs) (→Essential Characteristics) |
||
| Line 5: | Line 5: | ||
Cloud computing is a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management effort or service provider interaction. This cloud model is composed of five essential characteristics, three service models, and four deployment models. | Cloud computing is a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management effort or service provider interaction. This cloud model is composed of five essential characteristics, three service models, and four deployment models. | ||
| + | |||
| + | ==CA1 - Physical Server Hardware Research / Case study of one company that successfully migrated their on-premise network onto a public Cloud provider== | ||
| + | [[Media:Physical_Server_Hardware_Research-CA1_Cloud.pdf]] | ||
==Essential Characteristics== | ==Essential Characteristics== | ||
Revision as of 16:26, 6 June 2018
Media:Resumen_para_el_examen_cloud.pdf
Cloud computing refers to a utility-based provisioning of virtualized computa-tional resources over the Internet.
Cloud computing is a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management effort or service provider interaction. This cloud model is composed of five essential characteristics, three service models, and four deployment models.
Contents
- 1 CA1 - Physical Server Hardware Research / Case study of one company that successfully migrated their on-premise network onto a public Cloud provider
- 2 Essential Characteristics
- 3 Service Models
- 4 Deployment Models
- 5 Containers
- 6 Google Cloud Platform
- 6.1 Cloud SDK: Command-line interface for Google Cloud Platform
- 6.2 Crear una VM Instance
- 6.3 Crear storage
- 6.4 Connecting to Instances
- 6.5 Copy files
- 6.6 Firewall Rules
- 6.7 Cloud Storage FUSE: Mounting Cloud Storage buckets as file systems on Linux or OS X systems
- 6.8 Service Accounts
- 6.9 Live Migration of a Virtual Machine
- 6.10 Create Bitnami WordPress Site on Google Cloud
CA1 - Physical Server Hardware Research / Case study of one company that successfully migrated their on-premise network onto a public Cloud provider
Media:Physical_Server_Hardware_Research-CA1_Cloud.pdf
Essential Characteristics
On-demand self-service: A consumer can unilaterally provision computing capabilities, such as server time and network storage, as needed automatically without requiring human interaction with each service provider.
Broad network access: Capabilities are available over the network and accessed through standard mechanisms that promote use by heterogeneous thin or thick client platforms (e.g., mobile phones, tablets, laptops, and workstations).
Resource pooling: The provider's computing resources are pooled to serve multiple consumers using a multi-tenant model, with different physical and virtual resources dynamically assigned and reassigned according to consumer demand. There is a sense of location independence in that the customer generally has no control or knowledge over the exact location of the provided resources but may be able to specify location at a higher level of abstraction (e.g., country, state, or datacenter). Examples of resources include storage, processing, memory, and network bandwidth.
Rapid elasticity: Capabilities can be elastically provisioned and released, in some cases automatically, to scale rapidly outward and inward commensurate with demand. To the consumer, the capabilities available for provisioning often appear to be unlimited and can be appropriated in any quantity at any time.
Measured service: Cloud systems automatically control and optimize resource use by leveraging a metering capability1 at some level of abstraction appropriate to the type of service (e.g., storage, processing, bandwidth, and active user accounts). Resource usage can be monitored, controlled, and reported, providing transparency for both the provider and consumer of the utilized service.
On-Premise Computing:
- Requires hardware, space, electricity, cooling
- Requires managing OS, applications and updates
- Software Licensing
- Difficult to scale:
- Too much or too little capacity
- High upfront capital costs
- You have complete control
Cloud Computing:
- Shared, multi-tenant environment
- Pools of computing resources
- Resources can be requested as required
- Available via the Internet
- Private clouds can be available via private WAN
- Pay as you go
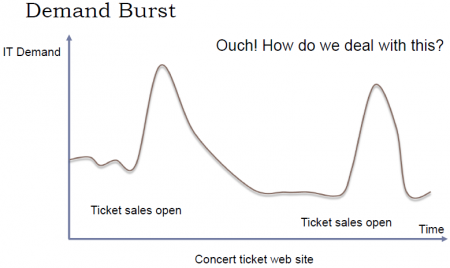
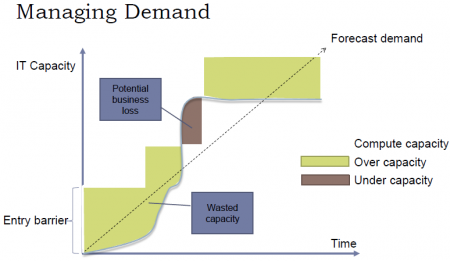
Una de las ventajas más importantes del Cloud es que puede ser «scaled» fácilmente (Resources can be requested as required). En otras palabras, a través del cloud la capacidad se puede variar fácilmente con respecto a la demanda. sólo cuando la demanda sea alta, el sistema será configurado para disponer de gran capacidad. On-Premise Computing, lo que generalmente pasa es que se configura el sistema para cubrir una capacidad promedio y generalmente se debe sobreestimar para que, cuando la demanda sea alta, poder todavía cubrirla. Entonces, cuando la demanda es baja estamos a "over capacity" y podría también pasar que cuando la demanda sea muy alta estemos a "under capacity". Esto es solucionado en el cloud. Esto se puede visualizar a través del ejemplo presentado en las siguientes figuras, en el cual se plantea el caso de un Concert ticket web site.
Service Models
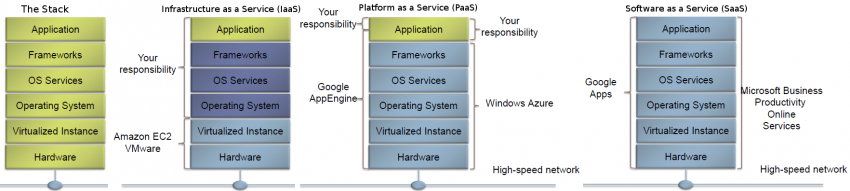
Infrastructure as a Service (IaaS) - Platform as a Service (PaaS) - Software as a Service (SaaS)
Software as a Service (SaaS): The capability provided to the consumer is to use the provider’s applications running on a cloud infrastructure2. The applications are accessible from various client devices through either a thin client interface, such as a web browser (e.g., web-based email), or a program interface. The consumer does not manage or control the underlying cloud infrastructure including network, servers, operating systems, storage, or even individual application capabilities, with the possible exception of limited user-specific application configuration settings.
Platform as a Service (PaaS): The capability provided to the consumer is to deploy onto the cloud infrastructure consumer-created or acquired applications created using programming languages, libraries, services, and tools supported by the provider.3 The consumer does not manage or control the underlying cloud infrastructure including network, servers, operating systems, or storage, but has control over the deployed applications and possibly configuration settings for the application-hosting environment.
Infrastructure as a Service (IaaS): The capability provided to the consumer is to provision processing, storage, networks, and other fundamental computing resources where the consumer is able to deploy and run arbitrary software, which can include operating systems and applications. The consumer does not manage or control the underlying cloud infrastructure but has control over operating systems, storage, and deployed applications; and possibly limited control of select networking components (e.g., host firewalls).
Deployment Models
Private cloud: The cloud infrastructure is provisioned for exclusive use by a single organization comprising multiple consumers (e.g., business units). It may be owned, managed, and operated by the organization, a third party, or some combination of them, and it may exist on or off premises.
Community cloud: The cloud infrastructure is provisioned for exclusive use by a specific community of consumers from organizations that have shared concerns (e.g., mission, security requirements, policy, and compliance considerations). It may be owned, managed, and operated by one or more of the organizations in the community, a third party, or some combination of them, and it may exist on or off premises.
Public cloud: The cloud infrastructure is provisioned for open use by the general public. It may be owned, managed, and operated by a business, academic, or government organization, or some combination of them. It exists on the premises of the cloud provider.
Hybrid cloud: The cloud infrastructure is a composition of two or more distinct cloud infrastructures (private, community, or public) that remain unique entities, but are bound together by standardized or proprietary technology that enables data and application portability (e.g., cloud bursting for load balancing between clouds).
Containers
https://www.cio.com/article/2924995/software/what-are-containers-and-why-do-you-need-them.html https://cloud.google.com/containers/
Containers are a solution to the problem of how to get software to run reliably when moved from one computing environment to another. This could be from a developer's laptop to a test environment, from a staging environment into production, and perhaps from a physical machine in a data center to a virtual machine in a private or public cloud.
Problems arise when the supporting software environment is not identical. For example: "You're going to test using Python 2.7, and then it's going to run on Python 3 in production and something weird will happen. Or you'll rely on the behavior of a certain version of an SSL library and another one will be installed. You'll run your tests on Debian and production is on Red Hat and all sorts of weird things happen."
And it's not just different software that can cause problems, he added. "The network topology might be different, or the security policies and storage might be different but the software has to run on it."
How do containers solve this problem? Put simply, a container consists of an entire runtime environment: an application, plus all its dependencies, libraries and other binaries, and configuration files needed to run it, bundled into one package. By containerizing the application platform and its dependencies, differences in OS distributions and underlying infrastructure are abstracted away.
Containers offer a logical packaging mechanism in which applications can be abstracted from the environment in which they actually run.
Google Cloud Platform
https://console.cloud.google.com
Go to Billing > Overview: para ver la Amount remaining del Promotion value of 243.35
Lo primero que tenemos que hacer es crear un proyecto. Generalmente hay un proyecto by default llamado «My First Project». Para crear un nuevo proyecto debemos ir a la pestaña que se encuentra justo al lado del Main Menu (Hamburger).
Cloud SDK: Command-line interface for Google Cloud Platform
The Cloud SDK is a set of tools for Cloud Platform. It contains gcloud, gsutil, and bq, which you can use to access Google Compute Engine, Google Cloud Storage, Google BigQuery, and other products and services from the command-line. You can run these tools interactively or in your automated scripts. A comprehensive guide to gcloud can be found in gcloud Overview.
Instalación
El proceso de instalación se encuentra detallado en https://cloud.google.com/sdk/
Logré instalarlo correctamente a través de la opción: Install for Debian / Ubuntu: https://cloud.google.com/sdk/docs/quickstart-debian-ubuntu
La procesimiento de instalación general para Linux: https://cloud.google.com/sdk/docs/quickstart-linux generó errores en mi sistema y no se pudo completar la instalación.
Initialize the SDK
https://cloud.google.com/sdk/docs/quickstart-linux
Luego de instalar SDK, debemos usar the gcloud init command to perform several common SDK setup tasks. These include:
- Especificar la user account (adeloaleman@gmail.com): authorizing the SDK tools to access Google Cloud Platform using your user account credentials
- Setting up the default SDK configuration:
- El proyecto (creado en al GCP) al que vamos a acceder by default
- ...
gcloud init
Crear una VM Instance
Main Menu (Hamburger) > Compute Engine > VM instances:
- Create Instance
Linux VM Instance
- Name: debian9-1
- Zone: Lo lógico es elegir la zona donde te encuentras, aunque si elijes alguna otra no habrá mucha diferencia (el precio varía dependiendo de la zona)
- Elegiremos la primera zona de West Europe propuesta: europe-west4-a
- Machine type: Is customize. Las características por defecto son:
- 1vCPU / 3.75 GB memory
- Las características más básicas son:
- micro (1 shared vCPU 0.6GB memory) (el precio baja considerablemente si elegimos éste) (para Linux podría ser suficiente)
- Container: Deploy a container image to this VM instance.
- Ver Containers
- No es, por ahora, necesario activar esta opción para nuestro propósito de prueba.
- Boot disk:
- OS: La opción por defecto es Debian GNU/Linux 9 (stretch). Vamos estar trabajando con éste.
- Disk size: 10GB por es la opción por defecto para Linux.
- Identity and API access :
- Service account: Esta opción se encuentra ajustada a "Compute Engine Default Service Account".
- Access scopes:
- Allow default access: Activada por defecto...
- Allow full access to all Cloud APIs
- Es apropiado marcar esta opción. Si no se marca no se podrá, por ejemplo, copiar files desde una VM instance a un bucket de esta forma:
gsutil cp file.txt gs://adelostorage/
- Otra opción es para permitir copiar archivos desde la VM hacia un bucket es configurar la "Service account". Debemos elegir una Service Account que hayamos configurade previamente para permitir este tipo de acciones. Ver Service Accounts para más detalles
- Set access for each API
- Firewall:
- Add tags and firewall rules to allow specific network traffic from the Internet
- Allow HTTP traffic: Activaremos esta opción to be able to maange the site through an SSH connection.
- Allow HTTPS traffic: Activaremos esta opción to be able to maange the site through an SSH connection.
- Management, disks, networking, SSH keys: Este link nos da la opción de realizar muchas otras configuraciones. Dejaremos todo por defecto por ahora.
Crear storage
Create a storage bucket:
Main Menu > Storage > Browser:
- Create bucket:
- Name: mi_storage-1
- Default storage class: Vamos a dejar la opción by default -- Multi-Regional
- Location: Europe
Connecting to Instances
https://cloud.google.com/compute/docs/instances/connecting-to-instance
Compute Engine provides tools to manage your SSH keys and help you connect to either Linux and Windows Server instances.
Connecting to Linux instances
You can connect to Linux instances through either:
- The Google Cloud Platform Console
- The gcloud command-line tool.
- Connecting using third-party tools
Compute Engine generates an SSH key for you and stores it in one of the following locations:
- By default, Compute Engine adds the generated key to project or instance metadata.
- If your account is configured to use OS Login, Compute Engine stores the generated key with your user account.
The Google Cloud Platform Console
Esta es un Console que pertenece a la GCP a la cual se accede a travé de una Browser window. Para abrirla vamos a:
- In the GCP (Google Cloud Platform) Console, go to the VM Instances page.
- In the list of virtual machine instances, click SSH in the row of the instance that you want to connect to.
The gcloud command-line tool
A través del comando gcloud (incluido en Cloud SDK) podemos acceder a la VM Instance desde el Terminal (Console) de nuestra computadora.
gcloud compute ssh [INSTANCE_NAME]
Connecting using third-party tools
https://cloud.google.com/compute/docs/instances/connecting-advanced#thirdpartytools
También podemos acceder a una VM Instance sin necesidad de utilizar herramientas de la GCP, como lo son The Google Cloud Platform Console or gcloud. Podemos, en su lugar, utilizar SSH.
You can access an instance by presenting your private SSH key file through a third-party tool. If you are on a Linux or macOS workstation, you can use the ssh command to connect.
The SSH command
- Provide your public SSH key to an instance using one of the available options.
- In the console, find the external IP address for the instance that you want to connect to. Go to the list of your instances.
- In a terminal, use the ssh command and your private SSH key file to connect to your instance. Specify your username and the external IP address of the instance that you want to connect to:
ssh -i [PATH_TO_PRIVATE_KEY] [USERNAME]@[EXTERNAL_IP_ADDRESS]
Providing public SSH keys to instances:
To connect a Linux VM instance, you need your own SSH key, which consists of a unique private SSH key file and a matching public SSH key file. SSH keys are created and managed for you whenever you connect using Compute Engine tools. However, to connect with third-party tools, you must provide your public SSH key to the instance using one of the following options:
Copy files
From the host computer to a bucket on Google Cloud
Luego de crear el bucket, podemos copiar archivos al bucket. Hay diferentes formas de hacerlo:
- Sinple drag and drop
- Usando el terminal de Google cloud
- Desde el terminal de la computadora luego de instalar Cloud SDK
Desde el terminal de la computadora luego de instalar Cloud SDK
El siguiente comando copia un archivo que está en mi computadora a un bucket on GC:
gsutil cp probando gs://adelostorage
Where adelostorage is the name of the bucket.
From the host computer to a Linux VM Instance or between VM's
https://cloud.google.com/sdk/gcloud/reference/compute/scp
To copy a remote directory, ~/narnia, from example-instance to the ~/wardrobe directory of your local host, run:
gcloud compute scp --recurse example-instance:~/narnia ~/wardrobe
From a bucket to an VM Instance
Luego de acceder a una VM Instance, puedo copiar un archivo desde un bucket a dicha VM Instance a través de la siguiente orden:
gsutil cp gs://adelostorage/probando.txt .
Firewall Rules
How to open a specific port such as 9090 in Google Compute Engine:
https://cloud.google.com/vpc/docs/using-firewalls
Por defectos, sólo el puerto tcp:80 se encuentra abierto. Los otros están protegidos por los firewalls. Si configuramos, por ejemplo, un Web Server (Apache, NGINX) en un puerto distinto al 80, debemos modificar los Firewall Rules para que el Web Server sea capaz de servir las páginas a través de otro puerto.
Para abrir un puerto vamos a:
- Choose you Project.
- VPC network > Firewall rules
- Create a firewall rule
- Choose Create Firewall Rule
Luego, seguir los pasos indicados en: https://cloud.google.com/vpc/docs/using-firewalls:
- Source IP ranges:
- If you want it to apply to all ranges, specify 0.0.0.0/0
- Specified protocols and ports:
- tcp:8080 (para abrir el puerto 8080)
Cloud Storage FUSE: Mounting Cloud Storage buckets as file systems on Linux or OS X systems
https://cloud.google.com/storage/docs/gcs-fuse
Cloud Storage FUSE is an open source FUSE adapter that allows you to mount Cloud Storage buckets as file systems on Linux or OS X systems.
Installing Cloud Storage FUSE and its dependencies
https://github.com/GoogleCloudPlatform/gcsfuse/blob/master/docs/installing.md
- Add the gcsfuse distribution URL as a package source and import its public key:
export GCSFUSE_REPO=gcsfuse-`lsb_release -c -s` echo "deb http://packages.cloud.google.com/apt $GCSFUSE_REPO main" | sudo tee /etc/apt/sources.list.d/gcsfuse.list curl https://packages.cloud.google.com/apt/doc/apt-key.gpg | sudo apt-key add -
- Update the list of packages available and install gcsfuse:
sudo apt-get update sudo apt-get install gcsfuse
- (Ubuntu before wily only) Add yourself to the fuse group, then log out and back in:
sudo usermod -a -G fuse $USER exit
- Future updates to gcsfuse can be installed in the usual way:
sudo apt-get update && sudo apt-get upgrade
Set up credentials for Cloud Storage FUSE
Cloud Storage FUSE auto-discovers credentials based on application default credentials:
- If you are running on a Google Compute Engine instance with scope storage-full configured, then Cloud Storage FUSE can use the Compute Engine built-in service account. For more information, see Using Service Accounts with Applications.
- Si se está usando una Google Compute Engine Instance, no se tiene que hacer nada para montar el Bucket. Sin embargo si el Access scopes de dicha Instance no fue configurado correctamente, entonces no podremos copiar arechivos desde la Instance hacia el Bucket montado. Ver en la creación de la VM Instance que es apropiado elegir "Allow full access to all Cloud APIs" o elegir una Service Account que hayamos configurade previamente para permitir este tipo de acciones. Ver Service Accounts para más detalles.
- If you installed the Google Cloud SDK and ran gcloud auth application-default login, then Cloud Storage FUSE can use these credentials.
- If you set the environment variable GOOGLE_APPLICATION_CREDENTIALS to the path of a service account's JSON key file, then Cloud Storage FUSE will use this credential. For more information about creating a service account using the Google Cloud Platform Console, see Service Account Authentication.
Mounting a Google Cloud Storage Bucket as a local disk
- Create a directory:
mkdir /path/to/mount
- Create the bucket you wish to mount, if it doesn't already exist, using the Google Cloud Platform Console.
- Use Cloud Storage FUSE to mount the bucket (e.g. example-bucket).
gcsfuse example-bucket /path/to/mount
Es muy importante notar que si montamos el bucket como se muestra arriba, no podremos accederlo a través del Web Brower. Es decir, el Web server no tendrá la permisología para acceder a este directorio.
Esto es un problema si queremos colocar un sitio web en el bucket; al cual se va a acceder a través de la VM Instance.
En este caso, debemos montarlo de la siguiente forma: https://www.thedotproduct.org/posts/mounting-a-google-cloud-storage-bucket-as-a-local-disk.html
sudo gcsfuse -o noatime -o noexec --gid 33 --implicit-dirs -o ro -o nosuid -o nodev --uid 33 -o allow_other mi_storage1 /path/directory/Explaining the mount options:
- ro - mount the volume in read-only mode
- uid=33,gid=33 - grant access to user-id and group-id 33 (usually the web serve user e.g. www-data):
- Your OS has a web server user whose user-id (UID) and groupd-id (GID) are 33
Para desplegar el web server user-id (UID) and groupd-id: http://www.digimantra.com/linux/find-users-uid-gid-linux-unix/
id -u www-data id -g www-data
- noatime - don't update access times of files
- _netdev - mark this as a network volume so the OS knows that the network needs to be available before it'll try to mount
- noexec - don't allow execution of files in the mount
- user - allow non-root users to mount the volume
- implicit_dirs - treat object paths as if they were directories - this is critical and Fuse-specific
- allow_other - allow non-root users to mount (Fuse-specific AFAIK)
- To unmount the bucket:
fusermount -u /home/shared/local_folder/
Service Accounts
A service account is a special account whose credentials you can use in your application code to access other Google Cloud Platform services.
Creating and Managing Service Accounts: https://cloud.google.com/iam/docs/creating-managing-service-accounts#creating_a_service_account
Creating and Enabling Service Accounts for Instances: https://cloud.google.com/compute/docs/access/create-enable-service-accounts-for-instances#createanewserviceaccount
Granting Roles to Service Accounts: https://cloud.google.com/iam/docs/granting-roles-to-service-accounts
Por ejemplo, para poder copar arvhivos desde VM Instance hacia un Bucket, you need to Setting up a new instance to run as a service account. Dicha service account tiene que haber sido Granted with the particular Roles que permiten dicha operación de copia.
To grant the roles, no puede hacerlo a través de la línea de comandos pues me generó un error. Lo pude sin embargo hacer desde la página de GCP. para la operación de copia descrita arriba hay que agregar a la service account en la cual corre la VM los roles relacionados con Storage:
- Storage Admin
- Storage Object Admin
- Storage Object Creator
- Storage Object Viewer
Luego de haber creado la Service Account podemos, al momento de crear la VM Instance, ajustar que la new instance runs as this service account (ver ).
Live Migration of a Virtual Machine
- The virtualBox machine that you migrate should be using a VMDK (Virtual Machine Disk), not VDI (VirtualBox Disk Image) or VHD (Virtual Hard Disk).
- Make sure you the NIC (Network Interface Controler) (Network > Adapter 1 > Attached to) is set to NAT so that you have Internet access.
- Es muy importante tomar en cuenta que para podernos conectar (a través de gcloud compute ssh VMmigrada) a la VM Instance luego de haberla migrado, el paquete openssh-server tiene que haber sido previamente instalado en la VM.
Para realizar la migración:
- In the GCP
- Main Menu > Compute engine > VM Instances: Import VM
- There you will be redirected to the Cloud Endure Platform (VM Migration Service)
- In the Cloud Endure Platform (VM Migration Service)
- https://gcp.cloudendure.com
- GCP credentials
- We need to create GCP credentials (Google Cloud Platform JSON private key (JSON file)). To generate a JSON private key file (could be also PKCS12 format) (Creo que estas credenciales cambiarían sólo si queremos realizar una migración hacia otro proyecto):
- Click "Find out where to get these credentials"
- Lo anterior abrirá la página de Documentation with a link to "Open the link of Credentials"
- Then, you need to choose the project: The target project where your VM will be migrate.
- Debemos copiar el Project ID porque luego lo vamos a necesitar en la Cloud Endure Platforme
- Click "Create credentials" and Select "Service Account Key" option
- Select the JSON option (for key type)
- The service account should be "Compute engine default service account"
- Then hit create: the JSON file will be downloaded to your computer.
- Luego, you go back to the Cloud Endure Platform (VM Migration Service)
- Enter the Google Cloud Platform project ID
- Luego cargamos el JSON file (Google Cloud Platform JSON private key). Then "Save".
- Replication settings
- Live migration target: Google EU West 2 (London)
- Hit Save replication settings
- Luego de esto: Project setup complete Congratulations!
- Your Live Migration Project is set up. So, the next step is to install the CloudEndure Agent on your Source machine.
- Install the CloudEndure Agent on your Source machine
- How To Add Machines: https://gcp.cloudendure.com/#/project/2be028cc-40ae-4215-ad2c-52e3ce4e325d/machines
- In order to add a machine to the GCP, install the CloudEndure Agent on your machine (your VirtualBox VM for example) (data replication (proceso de transferencia de la VM) begins automatically upon CloudEndure Agent installation).
Your Agent installation token: (este código lo genera automáticamente la Cloud Endure Platform (VM Migration Service. No sé si es diferente en cada migración.. Creo podría depender del proyecto; entonces debería cambiar si queremos migrar una VM hacia otro proyecto)
0E65-51C9-50EE-E20E-A583-9709-1653-BA57-457D-92BF-57B9-0DE2-22DC-EA11-3B80-81E6For Linux machines:
Download the Installer:
wget -O ./installer_linux.py https://gcp.cloudendure.com/installer_linux.pyAntes de ejecutar el siguiente paso tuvimos que instalar:
sudo apt-get install python2.7 sudo apt-get install gccThen run the Installer and follow the instructions:
sudo python ./installer_linux.py -t 0E65-51C9-50EE-E20E-A583-9709-1653-BA57-457D-92BF-57B9-0DE2-22DC-EA11-3B80-81E6 --no-promptFor Windows machines:
Download the Windows installer here https://gcp.cloudendure.com/installer_win.exe, then launch as follows:
installer_win.exe -t 0E65-51C9-50EE-E20E-A583-9709-1653-BA57-457D-92BF-57B9-0DE2-22DC-EA11-3B80-81E6 --no-prompt
- Data replication
- Data replication begins automatically once the installation of the CloudEndure Agent is completed. You will see able to see progress on the Cloud Endure Platform (VM Migration Service)
- Data replication es de hecho el proceso en el cual la VM es copiada hacia la GCP.
- Launch target Machine
- Luego de haberse completado la Data replication, se habrá creado una Instance en la página de VM Instace del correspondiente proyecto en la GCP. Esta Instace, cuyo nombre contiene "replicator" no será la VM Instance definitiva. Debemos entonces hacer click en "Launch target Machine" (aún en la Cloud Endure Platform (VM Migration Service)), lo cual generará la VM Instance en la correspondiente página de la GCP. Habrán entonces dos Instance en la Página de la GCP. En mi caso:
- ce-replicator-goo16-20eb5f29
- ubuntu-18932dd6
- Si hacemos cambios en nuestra Local VirtualBox VM, podremos actualizar la correspondiente Google VM Instance fácilmente haciendo click en "Launch target Machine" nuevamente. La ce-replicator-goo16-20eb5f29 creo que tiene la función de actuar en esta actualización.
Create Bitnami WordPress Site on Google Cloud
Revisar la guía que Michael puso en Moodle: 7-2 Create Bitnami WordPress Site on Google Cloud.pdf